Blog Details
Why CID and Government Offices Require a Hash Calculator
3–4 min read
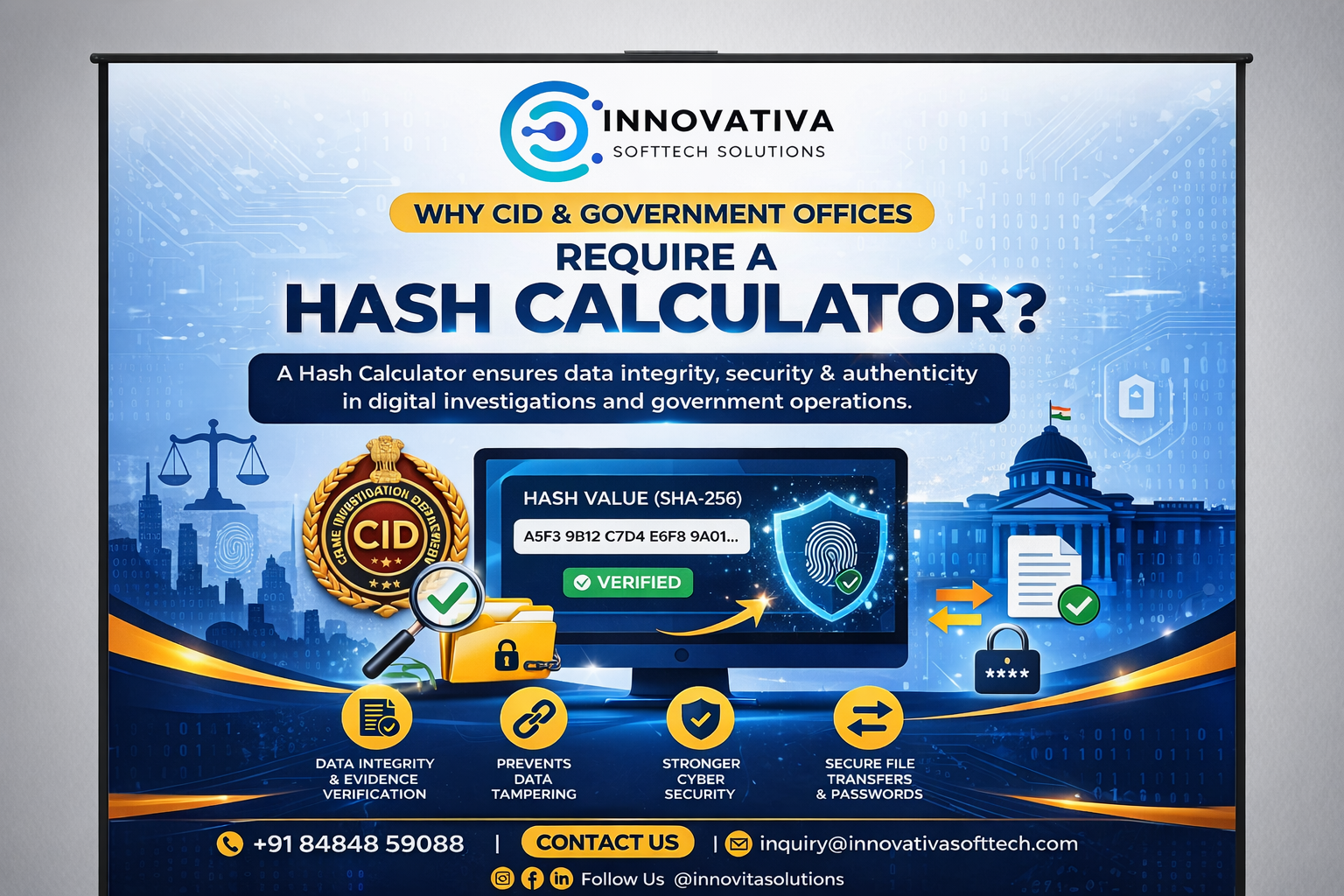
In an era where most information is stored, transferred, and analyzed digitally, maintaining the authenticity of data has become one of the biggest responsibilities for investigative agencies like CID and various government offices. A hash calculator plays a silent yet powerful role in this system by ensuring that digital data remains secure, unchanged, and legally valid.
A hash calculator works by converting any file—whether it is a document, image, video, or database—into a unique string of characters known as a hash value. This value acts like a digital fingerprint. The most important aspect of this fingerprint is that it is extremely sensitive to change. Even a minor modification in the file, such as adding a single character or altering a pixel, results in a completely different hash value. This characteristic makes hashing a reliable method to verify data integrity.
For CID departments, this becomes critically important during criminal investigations. Digital evidence such as call records, CCTV footage, emails, and forensic data must remain untouched from the moment it is collected to the time it is presented in court. If the integrity of this data is questioned, the entire case can weaken. By generating a hash value at the time of evidence collection and verifying it later, investigators can confidently prove that the data has not been altered at any stage. This process strengthens the credibility of evidence and supports a fair judicial process.
Government offices, on the other hand, deal with vast amounts of sensitive information, including citizen records, financial data, internal communications, and policy documents. In such environments, even a small unauthorized change can lead to serious consequences, including data breaches, fraud, or loss of public trust. Hash calculators help detect any such unauthorized modifications instantly. By comparing the current hash value of a file with its original value, officials can identify whether the file has been tampered with, ensuring transparency and accountability.
Another important aspect where hash calculators prove essential is during data transfer. Government departments frequently exchange files across different systems and locations. During this process, there is always a risk of data corruption or interception. By sharing the hash value along with the file, the receiving party can verify its authenticity. If the hash values match, it confirms that the file has been received exactly as it was sent, without any alteration.
Hashing also plays a crucial role in cybersecurity within government systems. Sensitive data such as passwords is never stored in plain text; instead, it is stored as hashed values. This ensures that even if a system is compromised, the actual data remains protected. Additionally, hash values are used to verify software integrity, helping detect malicious modifications or unauthorized updates.
In the context of digital governance and increasing reliance on e-governance platforms in India, maintaining secure and tamper-proof records has become a necessity rather than an option. Hash calculators support this transformation by enabling secure audits, ensuring compliance with legal standards, and building trust in digital systems.
In conclusion, a hash calculator is much more than a technical tool. For CID and government offices, it is a foundation for ensuring data integrity, strengthening cybersecurity, and maintaining legal credibility. As digital data continues to grow, the importance of hashing will only increase, making it an indispensable part of modern governance and investigation systems.
For More Knowledge :- https://innovativasofttech.com/index.html
